01. Technical Analysis: Web Account Manager (WAM)
The Web Account Manager (WAM) acts as the primary Authentication Broker in modern Windows versions. When signing into M365 applications (Teams, Outlook, Edge), WAM initiates a token flow that, by default, attempts to link the device identity with Azure AD.
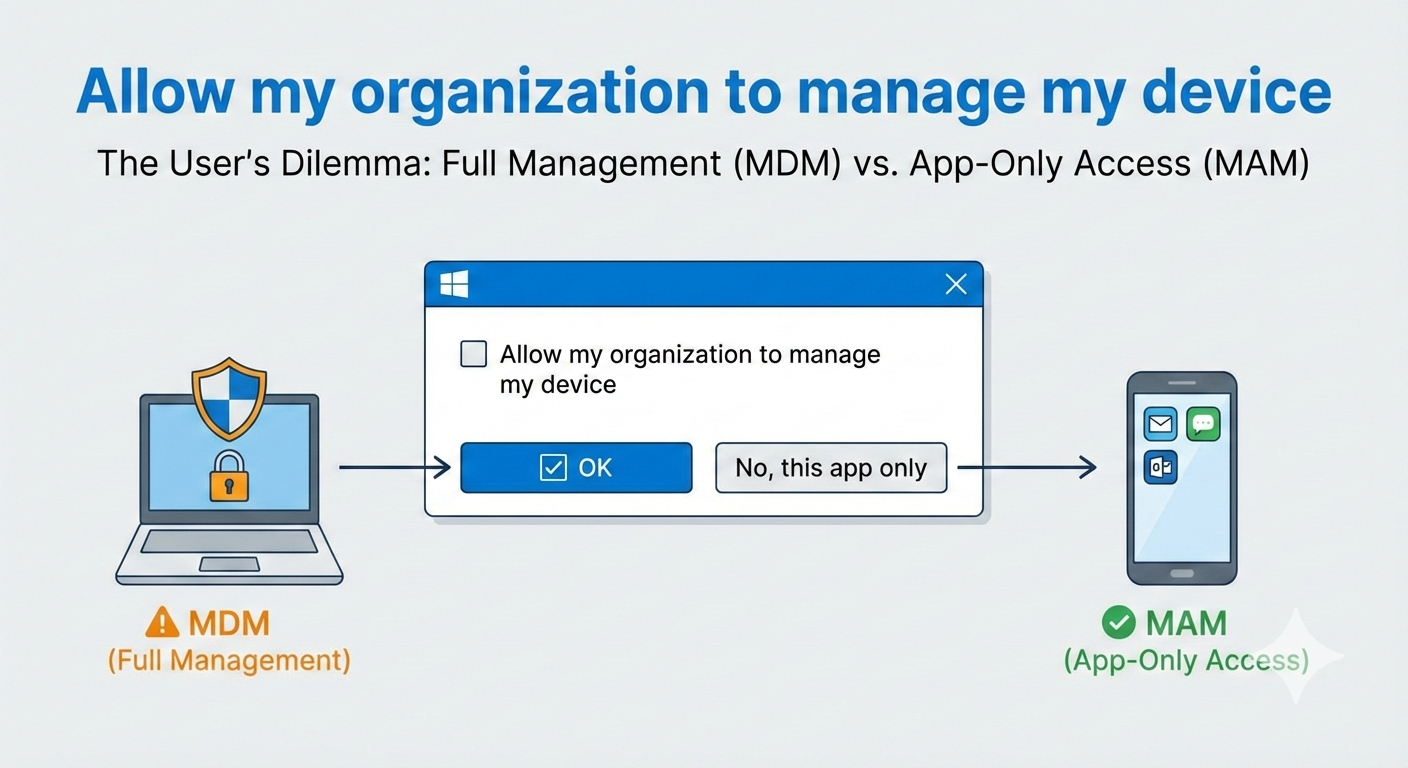
"Allow my organization to manage my device"
This process triggers two actions:
- Azure AD Registration: The device receives an identity in Entra ID.
- MDM Enrollment: If the user is licensed, an attempt is made to enroll the device into Intune.
02. Security Impact
From an Enterprise Architect's perspective, unmanaged enrollments introduce the following risks:
- Inventory Dilution (Shadow IT): Personal devices appear as "Registered" in Entra ID, distorting compliance reports.
- Support Overhead (Error 80180014): Properly configured Enrollment Restrictions block personal Windows devices. After confirming the dialog, the user receives an error message, generating unnecessary tickets.
- Conditional Access Inconsistency: Policies differentiating between "Browser" and "Desktop App" may trigger unexpectedly due to hybrid states (registered but not managed).
03. Method A: Intune Settings Catalog (Modern)
For corporate devices that are already managed, secondary accounts (e.g., test users or customer identities) should be prevented from affecting the MDM profile.
Configuration in the Intune Settings Catalog :
Path:
Administrative Templates \ Windows Components \ MDM
Setting:
Disable MDM enrollment when adding a work or school account
Value:
Enabled
04. Method B: Group Policy (Hybrid)
In hybrid environments (Active Directory Joined), GPO deployment is the standard method to stabilize clients before migrating to Intune.
Enable: Disable MDM enrollment
05. Method C: Registry Enforcement (Unmanaged)
For scenarios such as Kiosk systems, Admin Jump Hosts, or strictly isolated environments where absolutely no Azure AD Registration is desired, the dialog can be completely suppressed at the registry level. This technically enforces the "This app only" option.
# BlockAADWorkplaceJoin: Suppresses the dialog & AAD Registration
$regPath = "HKLM:\SOFTWARE\Policies\Microsoft\Windows\WorkplaceJoin"
if (!(Test-Path $regPath)) {
New-Item -Path $regPath -Force | Out-Null
}
New-ItemProperty -Path $regPath `
-Name "BlockAADWorkplaceJoin" `
-Value 1 `
-PropertyType "DWord" -Force
Write-Host "SUCCESS: Workplace Join Dialog is now blocked."06. Verification & Troubleshooting
After implementing the registry key or policy, verify the change via Event Viewer under
Applications and Services Logs > Microsoft > Windows > Workplace Join
.
Conclusion
Controlling the WAM enrollment dialog is critical for maintaining a clean device inventory and preventing Shadow IT. Whether through modern Intune policies, traditional GPOs, or registry enforcement, choose the method that fits your environment.
Need help with your M365 device strategy?
Request a Consultation